What is End User Computing (EUC)?
End User Computing (EUC) is a system in which individuals can create working applications beyond the divided development process of design, build, test, and release that is generally followed by professional software engineering teams.
EUC Use Cases & Advantages
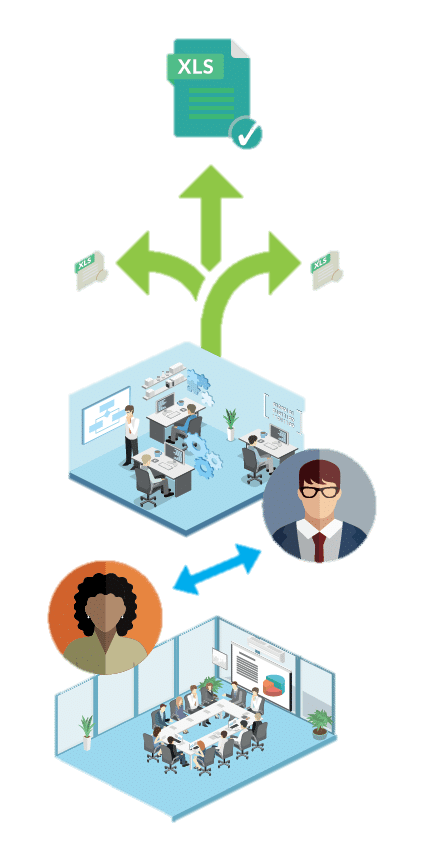
Microsoft Excel® is one of the most common examples of End User Computing platforms – readily accessible, fast, flexible, and familiar. Over time, EUCs have become essential to many financial operations, allowing users to manage and manipulate data quickly and efficiently. As such, End User Computing can be beneficial when faced with fast-changing regulations.
With the working environment in the midst of change, EUC is also becoming particularly prevalent in organizations with remote offices and BYOD users, ensuring business continuity even when organizations have to shift operations outside of their offices.
These features make End User Computing appealing and critical to business structures, but also make them difficult to manage and control. EUC applications aren’t subject to the same monitoring as traditional applications, and frequently management lacks visibility into how integral EUCs are within the company. So the advantages of EUCs have actually begun presenting risks to the businesses relying on them.
End User Computing risk
End User Computing risk is more prevalent than many might admit. Since data produced by EUCs is trusted by management and other end-users as a basis for integral business decisions and reporting, it’s essential that these EUC assets are effectively monitored and managed.
As End User Computing applications become more complex, the potential for EUC risk also increases. But as we’ve grown more accustomed to using spreadsheets to house confidential data, we’ve also become less aware of how these EUC tools come with risk.
When EUCs are critical to financial operations, if a spreadsheet or database has thousands of lines of code, receives data from other systems, uses multiple macros, or is not regularly reviewed, then you’re being exposed to EUC risk. You may not know if a change has taken place or data has been altered, regardless of whether that change is genuine, unintentional, or malicious.
Challenges & costs of End User Computing
Though EUCs are well-structured applications, within a business the knowledge of their existence or location can often be very limited. This means their value to the rest of the company isn’t easily accessible, leading to a number of potential costs of three main types:
- Direct costs: Direct costs and risks have a clear, measurable impact on a business’s finances. This can be through a spreadsheet error leading to a loss in revenue, or on a systemic basis as they contribute towards ongoing operational costs.
- Regulatory requirements: These costs are the result of two potential factors: the added operational processes to meet regulations or the failure to adhere to regulations, leading to fines and extended audits or external monitoring.
- Indirect costs: Indirect costs include things like reputational loss and are often the result of operational or financial incidents caused by poor EUC management. Reputational loss frequently affects all of the stakeholders of a business, including shareholders, clients, and auditors.
Learn how our clients use ClusterSeven for EUC Management
Click on the client logos below to see each Case Study.
EUC management: Assessing & controlling potential risk
End User Computing risk has been an issue for as long as Excel® Spreadsheets and Access® databases have existed. Any application that leaves system-based processes in the hands of an average user poses EUC risk.
Because of EUC risk and its potential for loss, there’s a real need for End User Computing management. Effective operational risk management means being aware of the potential for risk before it even occurs. To do this, it’s essential for organizations to have a structure to do the following:
- Define and establish what End User Computing risk is for the business
- Define what constitute high-risk EUCs
- Define additional EUC controls needed to manage the high risk
- Establish necessary reporting and monitoring processes for oversight
- Establish protocols for action in the case of rising risk levels or monitoring exposing exceptions
- Establish an appropriate response
This is a rough framework for managing EUC risk. All of it, though, must support the larger operational risk management framework. What are among the safest ways to manage and mitigate the risks of EUC applications? Taking a system-based approach to supporting the control framework, since a manual approach is inefficient and troublesome in cost-benefit and risk-reward.
The future of EUCs
With no sign that we’re lowering our dependence on EUCs, it’s vital for businesses to understand and assess their EUC risk. Despite the potential for extensive financial and reputational losses that End User Computing risk presents, it’s often not taken into account until too late.
Research provider Chartis estimated that the EUC Value at Risk for the 50 largest financial institutions was over $12 billion dollars, highlighting the degree to which End User Computing risk can impact a business. Beyond financial loss, EUC risk can lead to a number of other consequences, with one spreadsheet error resulting in junior doctors of Britain’s National Health Service losing their jobs.
Clearly, there’s much at stake when it comes to End User Computing risk. It’s critical that businesses assess, review and manage EUC risk…or else.

Manage your Shadow IT spreadsheets
With ClusterSeven, take control of the End User Computing assets hidden across your enterprise that can create hidden risk.